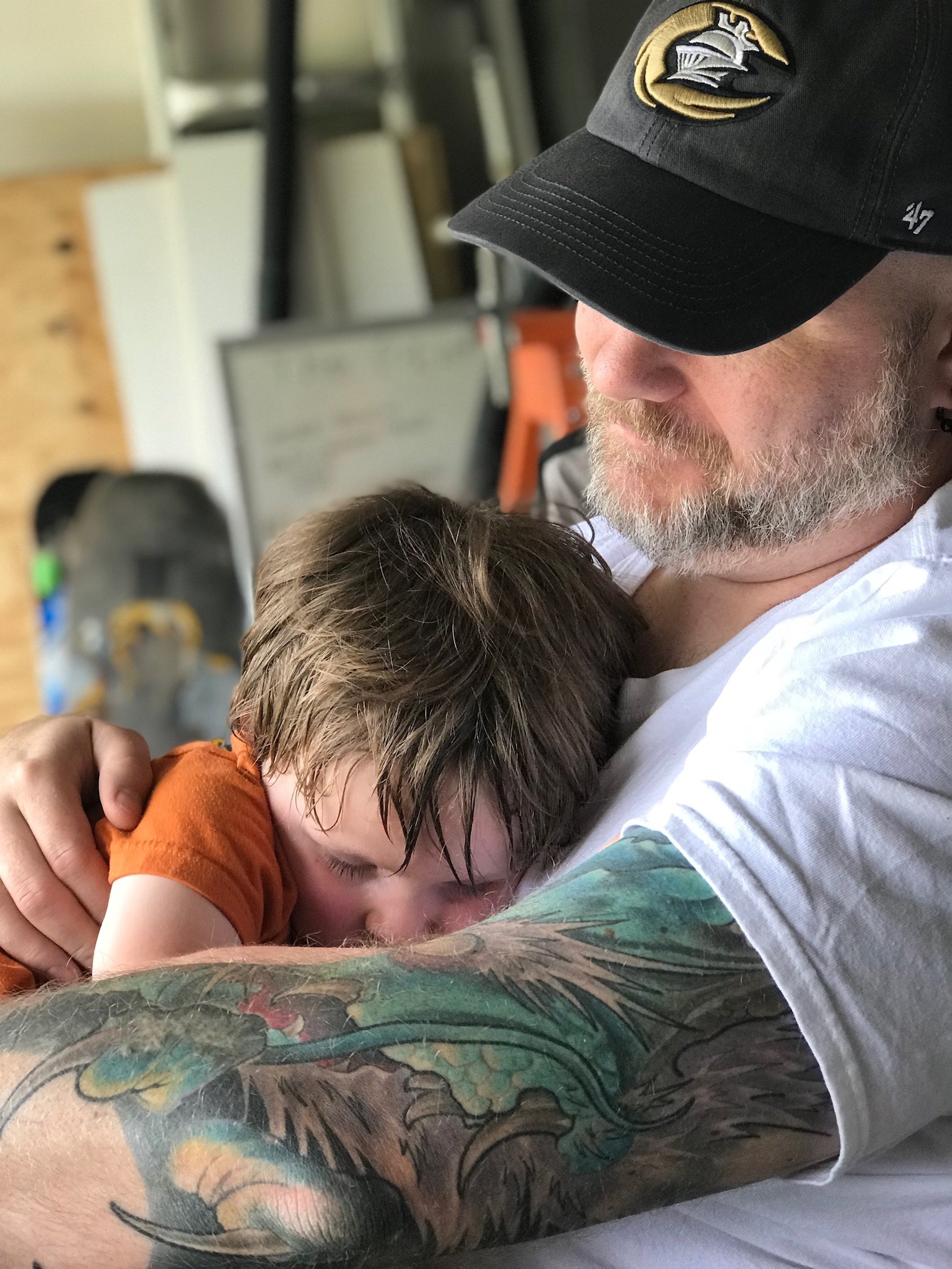
And on this day, I’m glad I only support an air-gapped Unix system.
“Air gapped”… in my day we called that the sneaker net.
Just remember to take off on 2038-01-19
Oh no, you misunderstand. I support a Unix system. Not Linux, not BSD, not Solaris. Y2K will be a problem in 2029 if don’t remember to set the clock back. Assuming the PDP-11 still works by then.
Does it not have epoch set to
1970-01-01 00:00:00? Or does the PDP-11 only use a non power of 2 number of bits, and you’ve already set the clock back before? Genuinely curious, never heard of 2029 problem before.Not a 2029 problem, maybe could have been clearer there. The clock is set 30 years behind. So, the clock will roll over to the year 2000 in 2030, meaning it will be a problem to address in 2029.
If only our vendors made Linux versions of their systems and regulators would approve them or the OS but no, my regulators only allow windows and approved software that they verify the hashes of every few months for changes
I am so lucky I didn’t update my PC
Do you use CrowdStrike on your PC? If not, you have nothing to worry about
I don’t so I’m good?
Yes.

Username kinda ckecks out
Sometimes you have to learn the hard way…
I’d laugh if this wasn’t affecting me directly.
I can laugh either for or at you, if you want.
I’ll pour one out for the frontliners.
I laugh and it does/did(over now) affect me. Bwahaha. Im getting work done and nobody can interrupt with email.
All I’ve noticed is that a lot of internet related things in my work are much faster today.
The schadenfreude could only be sweeter if my company used CrowdStrike on all the Windows systems. Then I really would have had a very peaceful focused day.
the good news is that it does make windows more secure. you cant hack something that has crashed.
Remember guys, it took about a decade for Solar Winds to discover somebody had root access to everybody that used their software, another decade for somebody outside Solar Winds to discover it and tell everybody, and half a decade with nobody claiming to have solved the issue up to now.
So when you believe that your computer with an EDS is safe just because you can’t use it, think again.
EDS?
It’s an oops.
It should be IDS.
That’s intrusion detection system, right?
Yep.
But there also exists Endpoint Detection and Prevention System, Intrusion Prevention System, Enterprise Security system, Network Threat Detection, Network Threat Prevention… And all those things name the exact same products (or at least, products you buy bundled on the same package).
Somehow I managed to use the one acronym that is wrong.
WAF is my favorite. It sounds so goofy.
Reminds me of a local cyber security firm, which declares war on a group of hackers. The CEO went on television to “double dog dare” the hackers to hack their servers and claim their firewalls are impenetrable.
Well you can guess the results, within 48 hours, their servers went down one after another. And when shit about to hit the fan, they literally turned off all of their servers for days. They hired a 3rd party IT firm to patch their security, then the CEO declared victory in a local newspaper.
And the hackers name? 4chan
Similar thing happened to the idiot CEO of Lifelock that used to advertise his actual social security number everywhere.
A smarter person would have used a fake SSN then claimed success when it never worked
I used to work at Equifax. LifeLock was the subject of many corporate trainings.
The most secure computer is the one not running any software. That’s why I recommend Crowdstrike.
Yeah, time to switch from CrowdStrike to SolarWinds…
 They stop breaches if nothing’s turned on. Roll safe (mode)
They stop breaches if nothing’s turned on. Roll safe (mode)The problem is the blind trust of these “vendors”
Decentralize control
Centralize control in house.
Compared to the status quo, that’s much more decentralized.
Ha guess why I’m on lemmy right now.
I really don’t want to be the guy responsible for this fuck up
This is an industry wide issue. This is just the first symptom.
What we need is to stop the blind trust
Yeah and that means they won’t nail some poor schmuck to the wall over this?
He’ll just get fired, apply somewhere else, and they’ll only know the dates he worked at CrowdStrike.
If anybody cared, they would have switched away from M$ by now.
For a company this big it would also have to have gotten past a code review and QA team, right? … right? …
Code review, QA team, hours of being baked on an internal test network, incremental exponential roll out to the world, starting slow so that any problems can be immediately rolled back. If they didn’t have those basics, they have no business being a tech company, let alone a security company who puts out windows drivers.
I like how they kept on pushing the update for hours
And who pushes out production updates on a Friday!
“Security”
We do.
“If something goes down over the weekend, fewer people see it” - my leadership team.
I guess Asia can report the problem on Sunday and I’ll get a nastygram and fix it that afternoon.
Of course, of course. This is how these things are always done.
Yeah, something this big is absolutely not one engineer’s fault. Even if that engineer maliciously pushed an update, it’s not their fault — it was a complete failure of the organization, and one person having the ability to wreck havoc like this is the failure.
And I actually have some amount of hope that, in this case, it is being recognized as such.
I agree but they will still blame it all on that one guy.
No they won’t, not if they’re in the slightest bit competent.
Blameless post-mortem culture is very common at big IT organizations. For a fuck-up this size, there are going to be dozens of problems identified, from bad QA processes, to bad code review processes, to bad documentation, to bad corner cases in tools.
There will probably be some guy (or gal) who pushed the button, but unless what that person did was utterly reckless (like pushing an update while high or drunk, or pushing a change then turning off her phone and going dark, or whatever) the person who pushed the button will probably be a legend to their peers. Even if they made a big mistake, if they followed standard procedures while doing it, almost everyone will recognize they’re not at fault, they just got to be the unlucky person who pushed the button this time.
The fact that random companies like Crowdstrike have kernel drivers in millions of computers they they ship remotely is a security risk in and of itself. We’re lucky crowdstrike just shipped a bug that crashes computers, other companies could have shipped a lot worse.
other companies could have shipped a lot worse.
other
companiesgovernments could have shipped a lot worse.FTFY
other
companiesgovernmentscould havemay have already shipped a lot worse.FTFY (high five!)
I’d swap may out for probably TBH.
I HATE UEFI I HATE UEFI I HATE UEFI
I HATE UEFI I HATE UEFI I HATE UEFI
So say, we all.
Why do you hate UEFI? Do you hate security?
Oh yeah, I really hate security. https://arstechnica.com/information-technology/2022/07/researchers-unpack-unkillable-uefi-rootkit-that-survives-os-reinstalls/
Sure, there are vulnerabilities. But UEFI offers features such as secure boot, which BIOS doesn’t. Also, its nice being able to boot from drives larger then 2tb.
More like ClownStrike.
Cloudstriked
They striked all right
Also: don’t trust your employees to boot into safe mode.
Trust a 3rd party to freely install system level files at any time.I knew how to fix the computers at work today in the morning, but we couldn’t get through to the help desk to get the bit locker codes for each computer until near the end of the day.
Also: don’t trust your employees to boot into safe mode. Trust a 3rd party to freely install system level files at any time.
Exactly. This is exactly the problem, and unless people wisen up the software security problem is only going to get worse. Companies and Governments need to rethink how they approach security entirely. This is a preview of what is to come, its only going to get worse and more damaging from here, and none of the vendors care.
Companies and Governments need to rethink how they approach security entirely. This is a preview of what is to come, its only going to get worse and more damaging from here, and none of the vendors care.
It is easy one for goverments. Ban security through obscurity. As well proprietary security software.
Moonbutt’s moonbuck))) Have I seen you somewhere?
Ban security through obscurity. As well proprietary security software.
The government likes proprietary software. They are never going to ban it.