For Android: learn the hard reset combo for your phone, especially if you encrypt it.
After rebooting, pattern/PIN will be required to decrypt the phone. Biometrics won’t work for this step. This is what graphene does for security, tries to keep the phone in a “before first unlock” state by rebooting on a timer. You can’t even read anything over USB/ADB, it’s scrambled until you unlock the phone.
The only drawback to just keeping your phone in this state is none of your apps are loaded, so no notifications/updates/processing at all.
Just power down your phone. No phone allows initial unlock with bio data
You don’t even need to do that. You can go to the power down menu on Android 14 and select lockdown. Even from the lock screen without unlocking the phone.
Thank you.
I’ve avoided willingly using biometrics so far. Though I’m sure our faces, gaits, body shapes, etc, are all stored somewhere, willingly or not.
Say no to biometrics. It’s like having a password you can never change.
Password you can never change
Not with that attitude! You can absolutely change your face. its rather inadvisable
Face… off…
So, it really depends on your personal threat model.
For background: the biometric data doesn’t leave the device, it uses an on-device recognition system to either unlock the device, or to gain access to a hardware security module that uses very strong cryptography for authentication.
Most people aren’t defending against an attacker who has access to them and their device at the same time, they’re defending against someone who has either the device or neither.
The hardware security module effectively eliminates the remote attacker when used with either biometric or PIN.
For the stolen or lost phone attack, biometric is slightly more secure, but it’s moot because of the pin existing for fallback.The biggest security advantage the biometrics have to offer is that they’re very hard to forget, and very easy to use.
Ease of use means more people are likely to adopt the security features using that hardware security module provides, and that’s what’s really dialing up the security.Passwords are most people’s biggest vulnerability.
I’ve read all this before. If you believe the people who designed and implemented the device and its myriad layers of firmware and software were 1. All acting in good faith and 2. Knew WTF they were doing… then: yes, sure.
Unfortunately that’s way too many strangers for me. Hundreds of people design and code these things. Meanwhile, every week there’s a clever new breach somewhere.
If you’re that afraid if the people who build phones, why are you ok with using any device that can access the internet?
I like how being cautious with my biometric data is beung framed as irrational fear and paranoia. As if ID theft never happens.
Using biometric data to unlock your phone does not make you more vulnerable to petty criminals.
While I do respect that viewpoint, there’s a lot more independent scrutiny of the hardware modules than there are around the parts that would handle any other authentication mechanism you might use.
Pixel phone example iPhone example
Just because something isn’t perfect doesn’t mean we should keep using the less good thing that it replaces.
Use the PIN if that’s more your cup of tea, just so long as you move away from passwords, since it’s the HSM that’s the protection, not the biometrics. Those are just to make it easier than passwords.
You can change PINs and passwords, but you cannot change your biometric data.
It’s about as smart as using your SSN as your username.
The point being that most people do not need to ever change their biometric data, because it isn’t used for remote authentication.
It’s about picking the right threat model, and for most people anything that gets them using the HSM is an improvement to their security.
Joke’s on them. My yo-yo diet keeps me safe from accurate body shape biometrics.
Same here. Still using the pattern lock. I’ve never used fingerprint not to even mention face scan.
it’s not a password; it’s closer to a username.
but realistically it’s not in my personal threat model to be ready to get tied down and forced to unlock my phone. everyone with windows on their house should know that security is mostly about how far an adversary is willing to go to try to steal from you.
personally, i like the natural daylight, and i’m not paranoid enough to brick up my windows just because it’s a potential ingress.
That’s why I put Linux on my house.
It’s not a great analogy. Your house and its windows are exposed to your neighborhood/community. Your internet device is adjacent to every hacker on the web.
it’s an analogy that applies to me. tldr worrying about having my identity stolen via physical access to my phone isn’t part of my threat model. i live in a safe city, and i don’t have anything the police could find to incriminate me. everyone is going to have a different threat model. some people need to brick up their windows
Assuming the phone’s security works as intended, what you’re saying is true. However, it’s a legit concern that the security is not airtight, and physical access is not actually required to harvest your biometric data.
I know the phone manufacturers make all sorts of claims about how secure biometric data is, but they have a profit motive to do so. I’m not being brick-up-my-windows paranoid by pointing out all the security failures and breaches we’ve seen over the years. Companies that have billions on the line are still frequently falling short at securing their own assets, much less their customer’s data.
I understand biometrics are convenient, and many folks love the ease / coolness factor of using them. Just don’t kid yourself that it’s secure by requiring your physical phone. Once the dark web has a digital copy of your biometric data, it’s compromised forever.
First provide proof that you can pull out biometric data out of a secure element in a phone.
That’s not retrieving the biometric data from the device, that’s retrieving the biometric data from surveillance or physical interaction.
It’s quite specifically the type of threat that most people do not need to worry about.
Last week, the 9th Circuit Court of Appeals in California released a ruling that concluded state highway police were acting lawfully when they forcibly unlocked a suspect’s phone using their fingerprint.
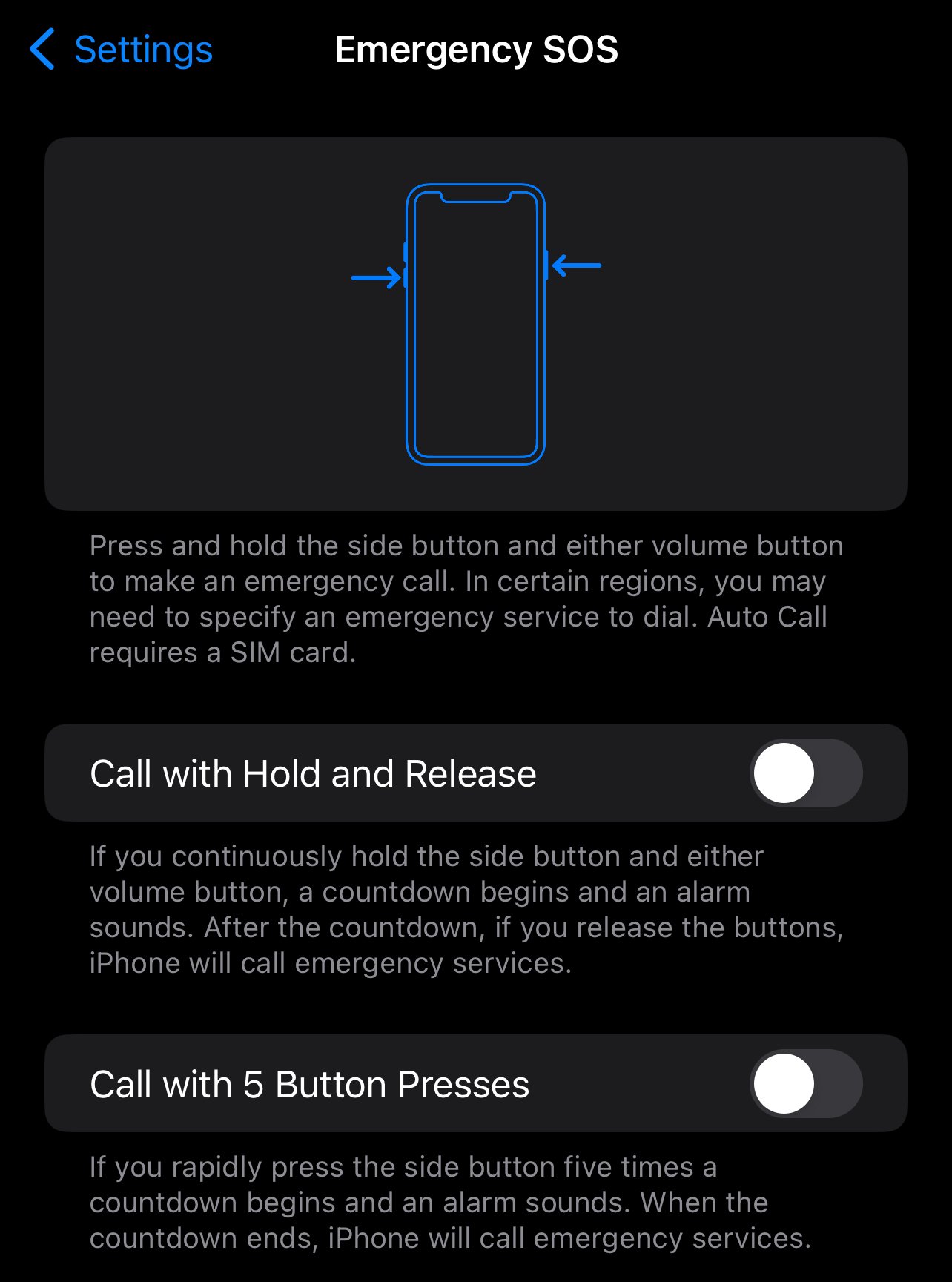
You can turn that and Face ID off on iOS by mashing the power button 5 times- it locks everything down.
Android has a similar feature. It’s called “Lockdown mode” on the shutdown menu. Locks the phone and turns off any biometric unlocks.
Except it doesn’t activate by mashing the power button 5 times. On my Pixel 8, that activates the emergency dialer that will automatically call 911 if you don’t cancel the prompt in 5 seconds. I did not know that before. Probably a better use for that feature. It also points out the different ideologies of Apple vs Android.
My wife’s pixel 3(?) with a flaky power button had us wake up to cops knocking on the door because of that feature.
You can turn it off somewhere in the settings
On iOS, for SOS, Medical ID, and “slide to power off” you hold power and a volume button. That also disables biometric ID.
Push and hold to get the power menu on my 7.
On my 8, that just activates the Google assistant. To get to the power menu, you have to press power (oddly named button, to be honest) and vol up at the same time. But these are active acts that you have to think about and verify to make sure they did what they are supposed to. Mashing the power button 5 times is succinct. I don’t have to guess how many seconds I’ve waited. I don’t have to feel to make sure I’m hitting the vol up instead of vol down accidentally. I count 5 times, 6 to make sure, and I can drop it while being certain that it’s going to call 911. That’s what I want in an emergency. A quick distinct action that requires no guessing to make sure it works. It makes sense once you stop and think. Nothing else about the power button makes sense, but at least that part does.
Try system - gestures - press power button. I have the choice of the power menu or the digital assistant.
I could do that…but then I lose easy access to the assistant. I could set up the tap on back function, but that doesn’t work when it’s in a holder in the car. There are no options that I can find that would let me assign the assistant to open on power + vol up. Unfortunately these phones aren’t as customizable as as I’d like them to be. Or at least not by default, but I don’t want to go through the trouble of flashing a new OS yet.
It does the same thing on iOS, but face/Touch ID is disabled after.
You can turn off the 911 “feature.” Don’t ask me how I know 😅
I was mowing my lawn and learned about that feature. A nice ladies voice came through my bluetooth headphones asking if I needed help lol. You can change what the button spam does and I changed it to call my mom instead.
On my Pixel 7 Pro, I press the power and volume up buttons simultaneously, then I can click Lockdown. Now my passcode is required to unlock the phone.
On my ditto (running GrapheneOS), the Lockdown option is accessible through the regular power button menu. When I press power+volumeUp it switches to silent mode. I don’t know if/where I changed this, since I can’t find the options when searching in settings.
EDIT: I just found it - in Settings > System > Gestures > Prevent ringing. I can either set power+volumeUp to mute the phone, or vibrate only. Nothing about the Lockdown option, but having it in the regular power button menu is good enough for me.
If by “regular power button menu” you mean holding the power button for a couple seconds, that was changed at least on pixel devices to bring up some bullshit called “Gemini”, some AI from googie that I never got a chance to say no to. Power + volume up is now how we get to the power menu, because of course they would change the function everyone uses occasionally to a more obscure combination without notice
In a getting pulled over situation, this works. But do it before you go protest anything. Or better yet, leave your phone at home. You don’t want to be reaching for something while a cop is pointing a gun at you and saying “Hands up!”
Not to mention it’s pretty regular to track who is participating by checking the towers in the zone all the people are participating.
Or get a geofence warrant
☞ EFF / Surveillance Self-Defense / Attending a Protest
Didn’t know EFF had this, neat
⚠️ WARNING: On android, mashing the power button 5 times calls emergency services…
Not on my Pixel 6. 🤷♂️ It just does what I told it to do, namely to open the camera.
Cool, you disabled the gesture. Clearly the default SO setting doesn’t apply to you…
I didn’t even know it existed. I had to search to find the setting, but I see it exists on my phone and it’s disabled. I don’t recall disabling it though.
Have to tried? On my Samsung pressing twice does the camera (as I’ve set it to) but doing 5 times tries to call emergency services.
I did, yeah. Gotta test before commenting, of course. I see I have the setting disabled for some reason. Don’t recall disabling it though.
They disabled it . I don’t understand why they even commented. It reads like some weird flex
I don’t know how it sounds like a weird flex. I was just asking. I don’t remember if it was something you could disable or not from when I had my pixel 5.
I didn’t even know it existed. I had to search to find the setting, but I see it exists on my phone and it’s disabled. I don’t recall disabling it though.
It’s not a flex… 🙄 I was just confused about how it seemed so established that this was an “Android” feature, so should be activated on my phone too, but it isn’t. And now that I see I have the functionality disabled but people say it’s the default, I’m even more confused because I don’t remember even seeing this setting. 🤷♂️
Right, correcting your incorrect information is “weird flex”. What are you, five?
On my Mi Max 3 it does not work as well. In “configure buttons” section of menu there is no call emergency number action, neither is there press [any button] five times trigger available. So clearly the function your phone has is not universal. What a wild world do we live in!
Thank you for defending me. ❤️ They were correct though. Apparently I had the setting disabled, but I don’t remember doing so. Must have been years ago on another phone? And then carried over when settings migrated? I don’t know when this feature was introduced. But yeah. It’s a thing.
But obviously not universal if you don’t have it. Which Android version are you on?
Which Android version are you on?
10 qkq1.190910.002
On android you can add a ‘lockdown’ mode to the power menu.
Thanks for this, didn’t know this was an option.
There are two ways you can do this on Android currently, but they’re not as quick. You can try to unlock with the wrong finger 5 times and it will stop allowing fingerprint unlocks. Or, you can hold down the power button for 10 seconds and the phone will reboot and also disable fingerprint unlocking.
That’s terrifying. So once we have tech to forcibly see inside the brain, that’s will be legal too?
“You shouldn’t be worried if you have nothing to hide” 🤷♂️
Tap for spoiler
/s
Probably. Wouldn’t it be good to have the truth during investigations?
However I think that we really need refine when warrantless searches can occur. Right now many searches seem to be done with very little evidence to justify them. I think this protection should apply to your mind and phone just like it applies to your house. This probably also needs to be considered at border crossings. Right now they have basically unlimited rights for searching what you have on you with little to no evidence.
We should probably also rethink about how the information is shared when there is a warrant. Right now during a trial a huge amount of personal information can be made available. Maybe if it was easier to get precise information less would be needed.
Wouldn’t it be good to have the truth during investigations?
Well, yeah, but the mind is fallible. That’s why eye witness testimony usually only gets a case so far, people tend to forget specifics and fill in the gaps without realizing they did.
That is important to remember but it is sort of orthogonal to the point being made. Assuming that mind-reading worked perfectly you can find the truth about what the person believes. In most cases if they think they murdered the person and the gun is hidden behind the oak in their backyard it is beyond a reasonable doubt. I think it is still useful to have the truth about what that person believes, even if we have to remember that their beliefs are fallible.
Not if it comes with a level of invasiveness that is unforgivable it wouldn’t be.
Forcibly invading someone’s mind after they were convicted beyond reasonable doubt would make you a monster.
Most trials and discoveries are already incredibly invasive. I don’t really see why the mind should be treated much differently. I would rather define what is acceptable evasiveness generally than different for mind vs written down in my diary.
Also why would you do this after they are convicted beyond reasonable doubt? This should only be done when required to reach the conclusion. Just like avoiding physical searches you can just plead guilty if you don’t want to be investigated.
If used properly this could actually be less invasive. Imagine a quick check of some facts that you believe with an automated machine that only returns the basic required information and you could be removed from the suspect list before other searches need to be done (like lawyers searching through your emails or personal notes).
I agree that this is a very dangerous thing to consider, and it needs to be applied very carefully. But I don’t think it is in the abstract any more morally wrong than the current methods of evidence gathering that we currently do. In many ways it could potentially be less harmful to the person being investigated. However it will be impossible to know for sure until we know how exactly this technology (when it is developed) works.
No, mind reading is a hundred orders of magnitude more invasive than any possible search.
There is no possible scenario where it could ever possibly be justified or excused. Your brain is unconditionally sacred. There is no possible theoretical version of such technology that could ever not be pure, unforgivable evil to use without completely uncoerced consent.
However I think that we really need refine when warrantless searches can occur. Right now many searches seem to be done with very little evidence to justify them. I think this protection should apply to your mind and phone just like it applies to your house. This probably also needs to be considered at border crossings. Right now they have basically unlimited rights for searching what you have on you with little to no evidence.
to be fair to the current justice system, a lot of times you can just hit the courts with “excuse me sir, this was unwarranted” and assuming it was actually unwarranted, they should overthrow it immediately.
Tou think it wouldn’t xD?
Came here to say that! Glad it’s getting around.
I’ve always wanted a setting to create a lockdown key and an unlock key. So something like middle-finger to unlock but index-finger to force it into PIN/password only mode. So you can have some convenience of a quick unlock but if an authority figure asks or forces you to unlock it you can one-tap lock it down.
That would be awesome.
In GrapheneOS, a single wrong fingerprint disables fingerprint unlock until the password is entered.
That’s not correct. It just says not recognized, and let’s you try again. I just tested it. Do you have documentation that it should work the way you said and mine is faulty?
Assuming you have the access to do this, e.g. awake, conscious, not handcuffed, etc. It’s safer to just always use a PIN in the first place.
You can also just long press a volume button with the lock button (with a FaceID phone). I find this harder to mess up under stress.
Do you have to mash it? Or will pressing it normally work?
Pretty sure Apple would replace the buttons with pressure sensors – not for user comfort but so that they are no longer replaceable with OEM parts and can be serialized. They did literally this with Macbook sleep sensors.
NO
The only thing I’ll mash is that subscribe button
On Graphene/Calyx you can auto-restart the phone after a given time period if it hasn’t been interacted with. Recommend turning this on for all users.
What’s the name of this feature for GrapheneOS? I’m not finding it.
Try searching for auto reboot, or some sort of extra security settings menu.
Just hold volume up and power for 3 seconds.
This is the best summary I could come up with:
Last week, the 9th Circuit Court of Appeals in California released a ruling that concluded state highway police were acting lawfully when they forcibly unlocked a suspect’s phone using their fingerprint.
The case didn’t get a lot of coverage, especially because the courts weren’t giving a blanket green light for every cop to shove your thumb to your screen during an arrest.
The ruling was also complicated by the fact that Payne was on parole at the time, back in 2021, when he was stopped by California Highway Patrol where he allegedly had a stash of narcotics including fentanyl, fluoro-fentanyl, and cocaine.
However, the panel said the evidence from his phone was lawfully acquired “because it required no cognitive exertion, placing it in the same category as a blood draw or a fingerprint taken at booking, and merely provided [police] with access to a source of potential information.”
The Electronic Frontier Foundation, a digital rights group, has offered guides for best practices when attending protests, and one of those is to turn off your thumbprint or face unlock before you hit the street.
“The general consensus has been that there is more Fifth Amendment protection for passwords than there is for biometrics,” Andrew Crocker, the Surveillance Litigation Director at the EFF, told Gizmodo in a phone interview.
The original article contains 988 words, the summary contains 217 words. Saved 78%. I’m a bot and I’m open source!
No.
Stop using biometrics period.
Why does this comic always give me Lain vibes
Further advice regarding civil disobedience:
LEAVE YOUR PHONES AT HOME. Write down some numbers in case you get arrested—or better yet, memorize them. There are journalists there for documenting. And there will be plenty of other people that don’t follow this advice. Leave anything they could use as leverage over you and your cohorts away. Don’t bring ID. Don’t bring anything except what you need for the action. It’s not worth the risk.
Maybe get a dumb burner phone with no personal data on it. You could potentially keep your main phone in a secret/secure pocket.
No. Several Jan 6 participants tried burners and they still got caught because the burners were still linked to their movements and activities and their personal phones were unusually unused/off/immobile for the amount of time the burners were used. You would have to expend a lot of effort to make sure your burner was completely disconnected from yours and your phone’s location, as well as making sure your phone showed signs of appropriate activity in your absence.
Not so easy.
keep your main phone in a secret/secure pocket.
Terrible idea, it will be found with absolute certainty if you’re arrested.
If you’re going somewhere where you think you might be at risk, IMHO, it’s probably just easier to turn your phone off. Android and iOS both require a non-biometric passcode after boot.
Or, if you want to keep your phone on, enable lockdown mode on Android, or tap power 5 times on iOS to require a non-biometric password at the next unlock.
It’s never a good idea to bring your phone with you. It can be used, even while powered off, to track and surveil you. The BLM protests were just the tip of the iceberg. The apps you have on your phone track you. The government is buying that tracking data. Your phone is a massive privacy weak point. It’s basically a bug you carry on you willingly. It’s not safe. Period.
https://www.vox.com/recode/22565926/police-law-enforcement-data-warrant
Leave your phone at home. It’s not worth it. It may not bite you in the ass the day of, but could very easily come back to haunt you after they investigate, in case anything goes “wrong” in their eyes. It’s just not worth it.
I think the fact that we are able to record everything that happens and automatically upload it seriously outweighs what you are saying.
The only reason cops get in trouble is only because people are filming. If it’s not caught on camera, it didn’t happen in the eyes of the law if it’s just our word against a cops.
It’s your life. This advice is important in more active circles. There are also jobs that should be given out. Just like there are medics that come out, there should be journalists—in leftist action circles, this isn’t EMTs and NBC photographers. See what I’m saying?
It’s ultimately your choice. But depending on what’s happening, the cause, the state, the cops, the current state of the govt of the country, etc., this advice can literally be invaluable.
For 200-250$ you can get very decent used compact cameras (like the RX 100). It won’t upload the photos immediatly, but it is still pretty much on par with most current cell phones.
It can be used, even while powered off, to track and surveil you.
How? The only legit thing I can think of is if they are tracking you anyway, and then they see your phone is turned off, they might try to claim that you must be up to something. But they won’t be able to track it while it’s off.
let’s put aside everything @Aceticon@lemmy.world wrote you; if the French state was trying to legalize exactly this, it must be possible: la validation pure et simple de l’activation à distance des fonctions de géolocalisation de téléphone et autres objets connectés (voiture, balises airtag, montre etc) qui repose exactement sur le même procédé technique que le dispositif censuré : la compromission d’un périphérique, en y accédant directement ou par l’intermédiaire d’un logiciel espion pour en prendre le contrôle à distance.
wasn’t the scandal about the Pegasus spyware all about this imperceptibility?
Nothing in your links above indicate that the spyware operates while the phones are powered off (although I relied on a crappy translation of the French). Could spyware mock the shutdown process so that it looks like the phone is powered off while the phone is actually running? Sure it can, but the victim will be tipped off when the phone’s battery is being drained even while it is “shut off”. (And someone who is paranoid enough to shut down their phone would pay attention to that.) . It seems like it’s not worth the effort.
read, listen to people that were spied on using the pegasus software. Easy to find
i don’t know if you’ve met any real activists, militants in your life but they’re rarely geeks. And checking the battery of their phone or reading about battery life isn’t one of their priorities
Yes, info on Pegasus is easy to find. And never says Pegasus is active when the phone is powered off. It’s undetectable and insidious in what it can grab, but at no point is there any reference at all to being active while the phone is powered off.
https://en.m.wikipedia.org/wiki/Pegasus_(spyware)
If you have a reference that states otherwise (that isn’t written by an AI), please supply it. I’ll be happy to give up on this if someone can prove their point.
And that is because it is way too easy to detect when the phone is off, not only because of the battery drain, but because the radios would be transmitting when they shouldnt . Plus, persisting across a reboot requires some trace of the Trojan to be on physical storage, which is more likely to be found on a scan.
I am assuming that when a state-level actor is hacking a phone, they are targeting a person directly, and know how to get the Trojan on undetected. Their main goal will be to continue to siphon data off it while it is in use. It’s not worth the risk of detection to track it while it is off (and not being used, after all.) Don’t you think they would prefer to use the same method they used the first time to infect the burner phone that’s actually being used?
If you can’t take out the battery, it’s never actually off.
That’s not quite how it works, though. These devices are basically mini computers now, there’s a limit to what they can do without fully booting. Devices that are plugged into the wall might be likely to retain some power-draining function while plugged in, but there’s only so much you can do on a trickle charge while a phone is powered off.
They’re still running in low power mode and can wakeup from the network so they can absolutelly be made to “boot up” without turning the screen on and you being aware of it.
This is not like a bloody PC were the lights turn on and you can hear the fans when the thing starts, it’s a machine with a low power mode in which it can already do a lot and which can be brought to a high power mode if needed without there being any visible or audible side-effects to alert the user.
Unless you completelly cut it off from power (by taking the battery out, which you can’t in most modern smartphones) that smartphone with the lights off, the screen off and making no sound at all can just as easilly be in low power mode waiting for you to press the On button, as it can be in full power mode with a mobile network connection active, accessing the microphone and the GPS microchip and sending that data out, and both will look exactly the same from the outside.
I think you are overestimating what these devices can do when turned off, specifically when whoever is doing the tracking wants to be covert. Devices like Cellular Radios and GPS chipsets are getting more efficient every year, but they still consume enough power that it would be noticed if they came on by themselves even if the device was off.
IMHO, as someone that works in security / privacy, I tend not to view it as a binary thing. It depends on where you live, what you’re protesting, what you look like, who you are, etc.
Are you in Russia or China and are protesting the government? Yeah, I might leave that thing at home. Are you a white lady in San Francisco marching with a pink knit cat hat during brunch hours, then you’re probably well on the other side of the risk spectrum. You might actually be introducing more risk by having less immediate access to communication or a camera.
IMHO, it’s nuanced.
The problem is that the people doing the surveillance are hardly going around honestly telling people what’s their surveillance profile.
For example in the UK that “pink knit cat hat white lady” would very likely be under surveillance if she was a member of the Green Party and participated in demonstrations. In fact, recently a number of cases came out where in the 80s and 90s the police had infiltrated Ecologist groups and even left some of the women in those groups pregnant with the children of men they late found out were undercover agents.
Further, the lower the barrier to entry to surveillance the lower the “threat profile” needed to end up under surveillance: if the authorities have already have well established and commonly used processes backed by ultra-broad surveillance court (or whatever those courts are called in your country) orders to just get from the mobile network providers all the phone numbers that connect to specific cell towers during a specific time period (such as the ones nearer a demonstration during that demonstratiom), pink knit cat lady is going to end up in the list just as easilly as baclava-wearing hard-core anarchist looking to break stuff.
They might not hack the pink knit cat hat lady’s mobile to install eavesdropping software, but she’s still in the list for every demonstration she attended carrying her phone and for the authorities finding out those who were at multiple demonstration and cross-searching with other databases to resolve those numbers to actual identities is pretty easy unless those people jumped through hops to keep those things disconnected (which, funny enough, smart anarchists are more likely to have done than your average pink knit cat hat lady)
We take on risk every time we decide to wake up and start the day.
I live in a place where I’m considerably more likely to get hit by a car while walking than thrown in jail as a political prisoner. That doesn’t mean I’m never going to go for a walk. I’m going to live life.
Leaving my phone at home seems pretty silly when the risk is very low in my nation and I do riskier things while cooking dinner.
I agree with your point, but balaclava is the hat, baclava is the delicious Greek pastry.

baclava-wearing hard-core anarchist looking to break stuff
what an image though 😁
The concern with bringing your phone is that police have subpoenaed cell providers to force them to turn over cell tower records. The police then used the lists of cell phones connected to those towers to track down protestors.
You shouldn’t bring your phone to a protest because it could end with police kicking your front door in three weeks after the protest has wrapped up.

And completely cover any tattoos. Even more identifiable than your face, honestly.
On pixel, if you’re ever need to - press and hold the power button, select “lockdown”.
(It might apply to other androids too, I don’t know.)
You will now need a pin to unlock the phone. This disables the lock screen shortcut (camera, light, etc) as well.
Why disable your convence features for an scenerio that is not likely and can be quickly and easily be prevented.
Universal: You could also just the tap the sensor with a “wrong” finger a few time, and the pin will be required.
Maybe don’t do this one in front the cops…if you find your self in a postion where they are trying to unlock your phone, you probably don’t want to piss them off. .
On my pixel 6 it is power + Volume Up to access the power menu with lockdown.
I also have a pixel 6 and holding down power also works, though you have to wait a second. Power and volume up is instant.
My power button long press only activates Google assistant, it never pops the power menu. Maybe it’s a setting somewhere.
Oh, yeah I think you’re right. I think I might’ve changed it at some point.
Just checked and it’s under system > gestures > press and hold power button
This was new info to me! Can confirm it works on a Pixel w/ GrapheneOS
The Pixel fingerprint scanner is so bad, you could end up locking it entirely by accident.
Behind-the-screen fingerprint scanners are an abomination.
Not my experience. They are usually instant, but you need a flagship device, of course. Otherwise it’s comparing apples and oranges.
My 5a sensor is fantastic (it is on the back). I’ll be sad when it’s time for this phone to go.
Behind-the-screen fingerprint scanners are an abomination.
Always reminds me of 1984’s telescreens. We’re almost there.
Mine works without issues since I removed the white circle and the unlocking animations.
It’s from AOSP, so any device close to the actual Android baseline should support that. This means that you can enter that mode from LineageOS as well.
On iOS just rapidly press the power button five times and it enters its lockdown state.
This isn’t new information. Might be a higher circuit reaffirming it though.
I am quite pleased that you are smarter than I am. I hope you get a nice cookie and cup of tea as your reward.
I don’t see it yet. When can I expect it in the mail?
IDK why I was an ass about it. Still good to spread the word.
It’s frustrating to no end that fingerprints and face ID are treated like passwords when they should be treated like usernames.
That makes a lot of sense !
They make sense as a 2FA. It would be really cool if I could require either PIN+fingerprint or a long recovery password.
## How to disable Face ID through the Power Off screen
- Hold down both the Side Button and either Volume Button at the same time for three seconds.
- The Power Off slider should appear. Tap Cancel.
https://appleinsider.com/inside/iphone/tips/how-to-quickly-disable-face-id
Real MVP right here. Good to know!
This is the advice people (with iOS) should follow, not disabling biometrics altogether. Using FaceID or TouchID prevents shoulder surfing to find out what the password to your phone is. When local passwords have so much control over a device, using biometrics to prevent anyone from seeing what your passcode is is very useful.
Those settings can also be altered under Settings > Emergency SOS
No.